For B2B SaaS companies, there is typically a strong desire for hypergrowth. Unlike a physical good or place, with SaaS, the ability to generate interest and acquire customers without constraints means that they can grow very quickly. That speed is what differentiates “hypergrowth” from “growth”. Hypergrowth companies are growing at 40% CAGR, moving quickly and adapting fast.

More growth, more problems?
Hypergrowth is the best problem to have; it simultaneously makes everything easier, and harder.
There are many articles out there with best practices on how to achieve hypergrowth, and most focus on things like building the right team, taking a Product Led Growth approach, or making analytics a key part of every decision you make. These best practices, however, rarely take into consideration a blessing and a curse of hypergrowth - especially on security and sales teams: the more customers and prospects you have in the pipeline, the more security reviews there are to respond to.
More customers in the pipeline mean more documentation to deliver, more security questionnaires to complete, and more processes to establish so you can make sure your program operates smoothly as things scale. To put it another way: if you have to complete questionnaires for approximately 50% of the customers in your pipeline, this is not a problem when you have 10 prospects. When you have 100, it becomes more of a problem. When you have 1,000, you better have a way to keep up.
Not only do you have to address more questionnaires as you grow your customer base, but you very likely will also have more certifications to achieve, more infrastructure to secure, and more people to manage. This makes it difficult for security teams to stay above water. Sales deals get slowed down, security gets pulled into proving security instead of securing things, and the whole program becomes more costly as people are hired to help the security team meet customer demands.
Scalability: a top priority of hypergrowth companies
Scaling efforts to build trust with customers around data security is a common challenge in hypergrowth companies. Scalability itself is one of the defining factors of what makes a hypergrowth company successful: finding ways to maximize the return on your activities, without having to scale your teams linearly.

Scalability and technology are the two highest priorities for hypergrowth companies. Finding ways to scale your team’s output (without a linear increase in team members) is crucial. Technologies that drive scale, foster collaboration and communication, drive down costs, and speed time to market are all critical to investigate & acquire in the early stages of company growth.
“Investing in the right technology” and “finding scalability” are easier said than done. Organizational and process changes need to be taken into account. These changes all get harder as the company gets bigger. Find the right scale and the right technology that help you become proactive in your trust-building efforts as early as possible is key.
“Our company is growing incredibly fast. If we don’t work smarter, the number of security questionnaires we receive would require us to pull security team members off of security tasks or create delays in responding that end up slowing the sales team down.”
Customer Trust and Privacy Lead, High growth SaaS company
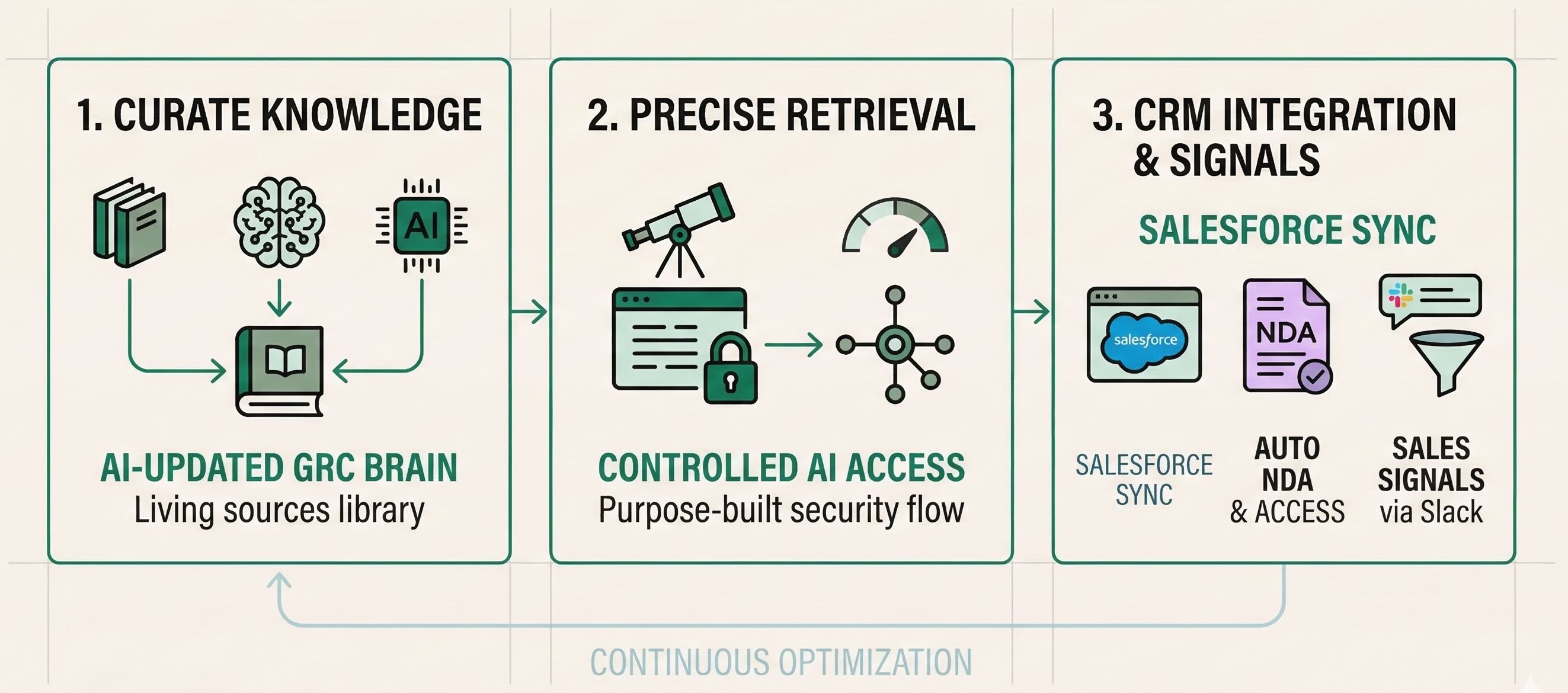
Customer Trust Program Growth Model
Below is a growth model of how to scale security and compliance operating practices and a detailed breakdown of each growth stage.

Pre-Growth Customer Trust
Before SaaS became the standard for internet businesses, it was common that, as a vendor, you wouldn’t receive a security review unless and until you started selling to larger companies. Back then it was only the largest companies digging into data security.
Now, entire companies are built on 3rd party SaaS tools and data security is more important than ever.
As your company starts out, your initial customers may ask about security. As you begin to grow, security expectations increase. When you are in a private beta and obtaining your first few customers, you may be able to satisfy questions from users by describing your security practices. Soon after that, your customers will likely build into a contract that you are obligated to achieve SOC 2 Type 2, ISO 27001, or some other standardized certification by a certain date in order to keep their business. And new prospects will require these certifications when considering whether to do business with you.
Growth: Reactive Approach
As your security and compliance procedures mature, you’ll find that it becomes easier to understand and respond to customer security reviews. You’ll have more documentation to share (such as compliance certifications, penetration test reports, backup and recovery procedures, etc) to provide assurances upfront. Don’t be surprised when that’s not enough, though. Many companies will still send along a custom security questionnaire, sometimes with a few dozen questions, other times exceeding 300 questions.
Growing and accelerating growth with a reactive approach quickly becomes costly as you are unable to anticipate and allocate resources based on the variability. This can lead to inefficiencies on the security team, and delays in the sales cycle, both of which introduce business challenges.
Growth: Proactive Approach
Reactively responding to security reviews only scales to a certain point. As you bring on more customers, and/or you expand into customers in a higher tier or specialized industry (i.e. Financial Services, Healthcare), the rigor of your security reviews will also increase. A reactive approach no longer makes sense; it’s not scalable or predictable.
The best approach is to be proactive in sharing your security posture early in the sales conversation, and with as little manual effort as possible. Companies like Segment are sharing their security documentation earlier in the sales cycle to avoid delays in the sales process and bypass the need for lengthy security reviews and custom questionnaires.
If you go to PagerDuty’s public security website, they provide a link for you to request access to their security documents, allowing prospects to self-serve the documentation they need. In a world where consumers are so used to accessing data on their own without the intervention of a person, this approach just makes sense. It gives prospects the ability to self serve, giving them a feeling of power and accessibility. In addition, PagerDuty’s security team can securely share their documents with an NDA and watermarking, allowing for a better user experience as well as automating work previously manual work.
Another tactic to consider when adopting proactive Customer Trust activities is to provide answers to commonly asked security questions on your website, or by providing updated FAQ documentation to your sales team. Some prospects will still submit a questionnaire, but by being transparent upfront you can avoid some of the back-and-forth, as well as get the conversation going sooner rather than in the latest stages of the sale.
Growth: Segmented Approach
Companies that are growing quickly and are very mature in their customer trust programs often develop a tiered approach that addresses security reviews differently depending on the size of the contract value. Allowing prospects with low ACV to submit a security questionnaire can lead to an imbalance in resources spent versus income gained. To ensure that valuable security resources are appropriately applied, many companies will set thresholds of contract value and allocate security resources based on those thresholds.
Operating in this model, the highest value customers get the full availability of resources to ensure they get their security assessment completed. This could include self-serve access to documents as well as frequently asked questions and answers, a response to their custom security questionnaire, and the ability to request custom documents and information. For medium-high value customers, it’s common to allow them to send their questionnaire only after they’ve attempted to use the self-serve information available to complete their review on their own. Contract values on the low range will typically get self-serve information and existing security documents for them to answer their security questions on their own. Security team resources are not “deployed” for these lower-tier customers.

Scaling Customer Trust - Best Practices
As your company grows, handling security requests manually and reactively simply won’t work. The process of building trust will use up too many resources, take too long, and become too costly. Moving to proactive and segmented approaches to customer trust is the only way to keep up with growth.
Some best practices to keep in mind as you think about scaling your security program:
- Sharing sensitive information in an insecure environment defeats the purpose of building trust with customers around your data security. A solution that handles NDA signing and watermarking will help you respond to reviews without compromising your security goals.
- Getting in front of requests for documents is simply not enough. Security questionnaires are so common these days that you need a solution to help customers self-serve answers to their questionnaires.
- For your high-value customers that you do accept a security questionnaire from, you need a solution that allows you to quickly respond with accurate and up-to-date information.
Not being able to keep up with an influx of new customers is a great problem to have, but it is still a problem. Every B2B company, regardless of the stage of growth, is going to be faced with the challenge of proving its security posture to current and prospective customers. At Conveyor we have several solutions, for companies of all stages of growth. Check out our pricing page if you want to see the different components of our solution, or sign up for free to test out our software and see how it can serve your needs, whatever they might be.
Here’s to fewer growing pains, and more customer gains!





.png)
.jpg)

.png)


.png)



































.png)










